St. Jude Takes Steps to Secure Vulnerable Medical Implants
Last week medical device maker St. Jude Medical provided security patches and guidelines necessary regarding vulnerabilities in its Internet connected medical devices that were uncovered this summer. You can read the original report from investment research firm Muddy Waters Research here.
The disclosure of the vulnerabilities created quite the ruckus in the financial markets and among security experts. See Michael Kan’s story, Medical device security ignites an ethics firestorm.
Now, with last week’s announcement from St Jude Medical the posturing is settling down as the company took steps to improve the security within the implantable device remote monitoring system Merlin@home Transmitter. “As technology evolves, St. Jude Medical made seven software updates in three years to the Merlin@home™ transmitter alone, and it will immediately release its latest software update to Merlin@home™, which will begin to be implemented today. The update includes additional validation and verification between the Merlin@home™ device and Merlin.net. St. Jude Medical has collaborated with the FDA, DHS ICS-CERT and other regulators in implementing this update. The company also plans to implement additional updates in 2017,” the company said in the statement.
“As medical technology advances, it’s increasingly important to understand how innovation and cyber security impact physicians and the patients we treat,” said Dr. Leslie Saxon, chair of St. Jude Medical’s Cyber Security Medical Advisory Board. “We are committed to working to proactively address cyber security risks in medical devices while preserving the proven benefits of remote monitoring to assess patient status and device function,” the company continued.
St. Jude’s announcement and updates were coordinated with statements from both the U.S. Department of Homeland Security Industrial Control Systems Cyber Emergency Response Team and the U.S. Food and Drug Administration (FDA). Their respective security guidance targets the patient, caregiver, provider constituencies.
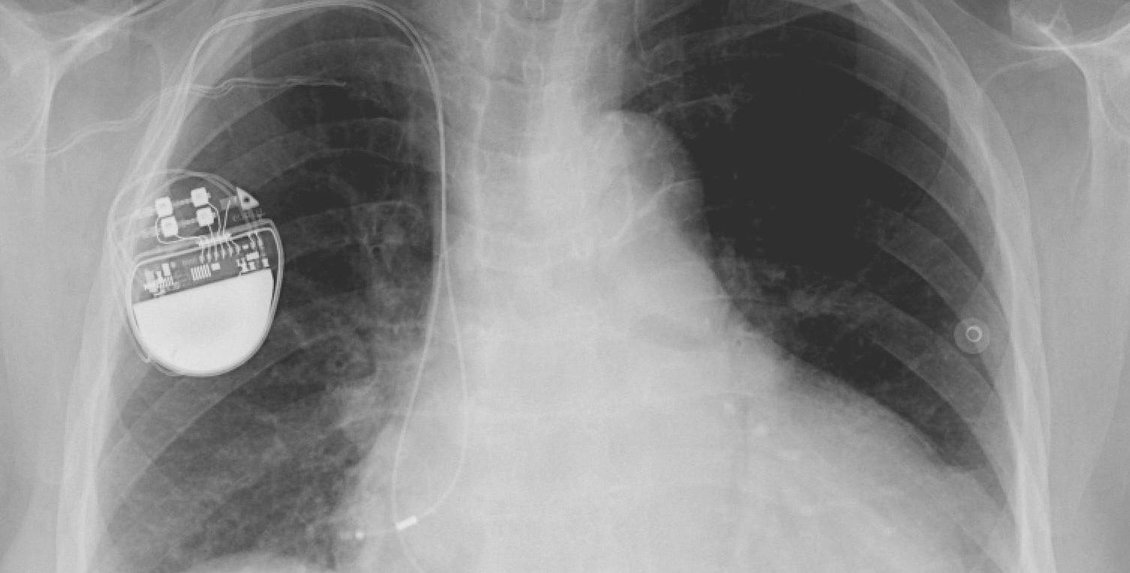
While St. Jude Medical had downplayed the risks associated with these vulnerabilities, the review of the equipment by the FDA found the flaws uncovered in the Merlin@home Transmitter the flaws, if successfully attacked, could allow unauthorized users to remotely access an RF-enabled implanted cardiac device the FDA wrote in their statement. “The altered Merlin@home Transmitter could then be used to modify programming commands to the implanted device, which could result in rapid battery depletion and/or administration of inappropriate pacing or shocks,” the FDA said.
Last week’s announcement from St. Jude Medical follows the FDA’s recent release of more general rules and guidelines aimed at medical device makers that will hopefully help manufacturers to better design, build, and manage devices that are reasonably safe from attack. As we covered in our post, FDA Prescribes Safer Path for Connected Medical Devices the FDA details: that medical device manufacturers should implement a structured and comprehensive program to manage cybersecurity risks. This means manufacturers should, among other things:
Have a way to monitor and detect cybersecurity vulnerabilities in their devices
- Understand, assess and detect the level of risk a vulnerability poses to patient safety
- Establish a process for working with cybersecurity researchers and other stakeholders to receive information about potential vulnerabilities (known as a “coordinated vulnerability disclosure policy”)
- Deploy mitigations (e.g., software patches) to address cybersecurity issues early, before they can be exploited and cause harm
The FDA said, in its statement, that it will continue to assess new information concerning the cybersecurity of St. Jude Medical's implantable cardiac devices and the Merlin@home Transmitter and provide updates if warranted. Additionally, the FDA wrote that it “reminds patients, patient caregivers, and health care providers that any medical device connected to a communications network (e.g. wi-fi, public or home Internet) may have cybersecurity vulnerabilities that could be exploited by unauthorized users. The increased use of wireless technology and software in medical devices, however, can also often offer safer, more efficient, convenient and timely health care delivery.”
That sounds like exceptional advice to me as while the benefits to the marriage of IoT and healthcare are clear, the fact that the risks and cyber threats to this coupling are going to be around for some time is just as clear.
tags
Author

George V. Hulme is an internationally recognized information security and business technology writer. For more than 20 years Hulme has written about business, technology, and IT security topics. From March 2000 through March 2005, as senior editor at InformationWeek magazine, he covered the IT security and homeland security beats. His work has appeared in CSOOnline, ComputerWorld, Network Computing, Government Computer News, Network World, San Francisco Examiner, TechWeb, VARBusiness, and dozens of other technology publications.
View all postsRight now Top posts
FOLLOW US ON SOCIAL MEDIA
SUBSCRIBE TO OUR NEWSLETTER
Don’t miss out on exclusive content and exciting announcements!
You might also like
Bookmarks







