EDR for Everyone
“EDR is the worst form of endpoint security except all the other endpoint security approaches that have come before it.”
The Last One Percent
We’ve all seen the headlines. Big name breaches. Confidential company and customer data exfiltrated. Highly sophisticated attacks, sometimes even nation-state sponsored - these are the crème de la crème of malware. They represent the last one percent of attacks that many of the traditional endpoint security products (aka signature-based prevention or Big Antivirus) that are currently in deployment in most enterprises have been unable to block. A number of other ancillary endpoint-based products – anti-exploit, tunable machine learning - have been created to close the prevention gap, but the real sophisticated attacks have still been able to elude these defenses.
The Emergence of EDR
Now, a new entrant technology – Endpoint Detection and Response, or EDR - has emerged based on a fundamentally different premise, that it is not possible to prevent 100% of all threats. EDR’s focus is on providing early detection and minimizing the dwell time of infections and subsequent damage. This is a refreshingly different approach but before the hype cycles kick into overdrive, we need to clarify how it can work in the real world.
EDR in the Real World
Can EDR replace all other endpoint security solutions before it? Definitely not. This is like using your elite swat team to fight street crime; not only is this expensive, it will also take the focus away from the real threats that needs the attention. Do we instead layer a pure play EDR on top of Big Antivirus, plus the anti-exploit tool and any other babelesque agents we’ve got on our endpoints? Companies have attempted to do that and some have experienced success, especially in organizations with well-resourced SOCs already in place. But it has not been for everyone. Managing multiple agents adds management complexity and with EDR typically being noisy, an already over-burdened and under-resourced IT team will be forced to make ill-informed incident investigation decisions from simply ignoring alerts to whitelisting applications in broad strokes that compromise the network, and the investment decision for EDR in the first place.
EDR for Everyone
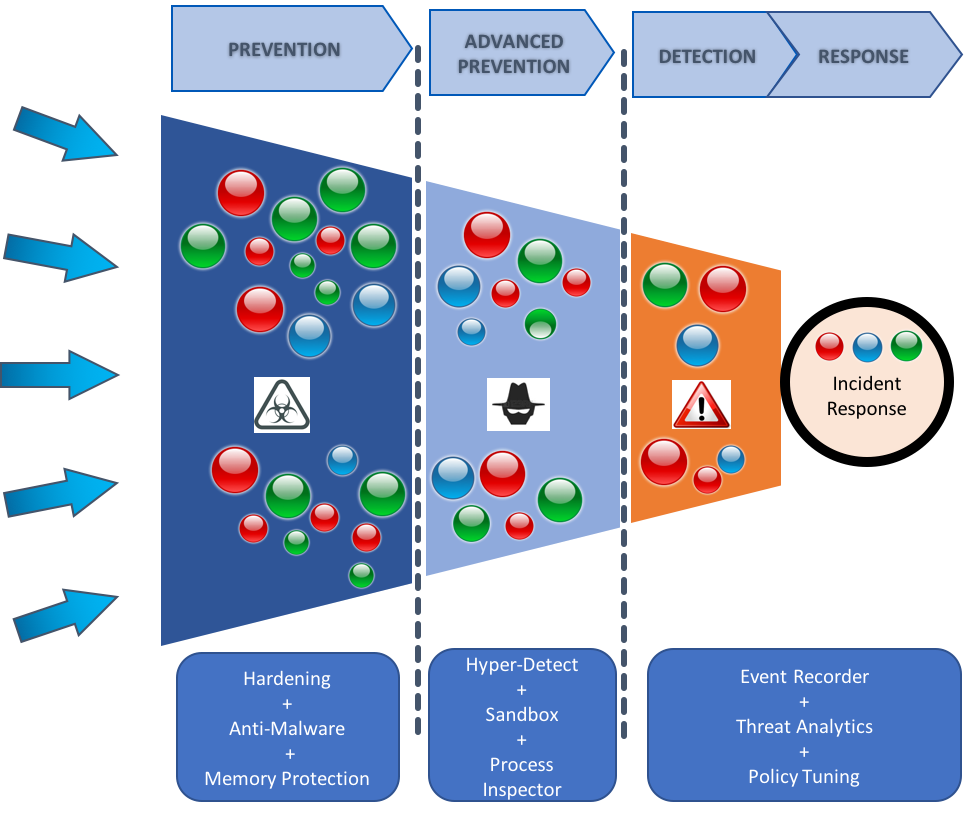
There is another way that we believe will help improve the viability of EDR for endpoint security, and not just for the “rich” organizations with well-funded well-resourced SOCs in place. EDR should not be let loose having to sift through everything unaided. Instead, if a funnel-based approach is employed, with preventative controls such as machine learning and behavioral monitoring at the front end of the attack monitoring cycle, a high percentage of known black can be eliminated from the equation and the EDR layer can be directed towards the narrow grey end of the funnel, allowing for a much higher level of fidelity in incident investigations. If the EDR and prior prevention layers are also part of the same integrated solution, it allows current IOC verdicts from the EDR ‘module’ to train the prevention layers in effecting future detections at pre-execution itself. In other words, to stay ahead of these highly sophisticated and elusive threats and allow EVERYONE to benefit from the value of EDR requires an integrated prevent-investigate-detect-respond solution. It has the effect of reducing unnecessary noise from false alarms or trivial threats, and allows the EDR layer to focus on the real and dangerous.
GravityZone XDR
We’ve built out our endpoint security solution on the basis of the above vision of ‘EDR for Everyone’. Today, we are proud to announce the release of GravityZone XDR – Bitdefender’s endpoint security platform that combines all of its signature-less pre-execution and on-execution preventative controls with early detection and response capabilities - all available in one agent and one console.
GravityZone XDR (part of the GravityZone Ultra suite) is based on an integrated prevent-detect-investigate-respond-evolve approach to endpoint security:
Prevent: block all known bad and a high percentage of unknown bad at pre-execution layer itself without saturating the EDR analytics engine with unnecessary noisy incident alerts
Detect: supported by built-in intelligence from threat protection engines and analysis of a stream of behavioral events from an endpoint event recorder
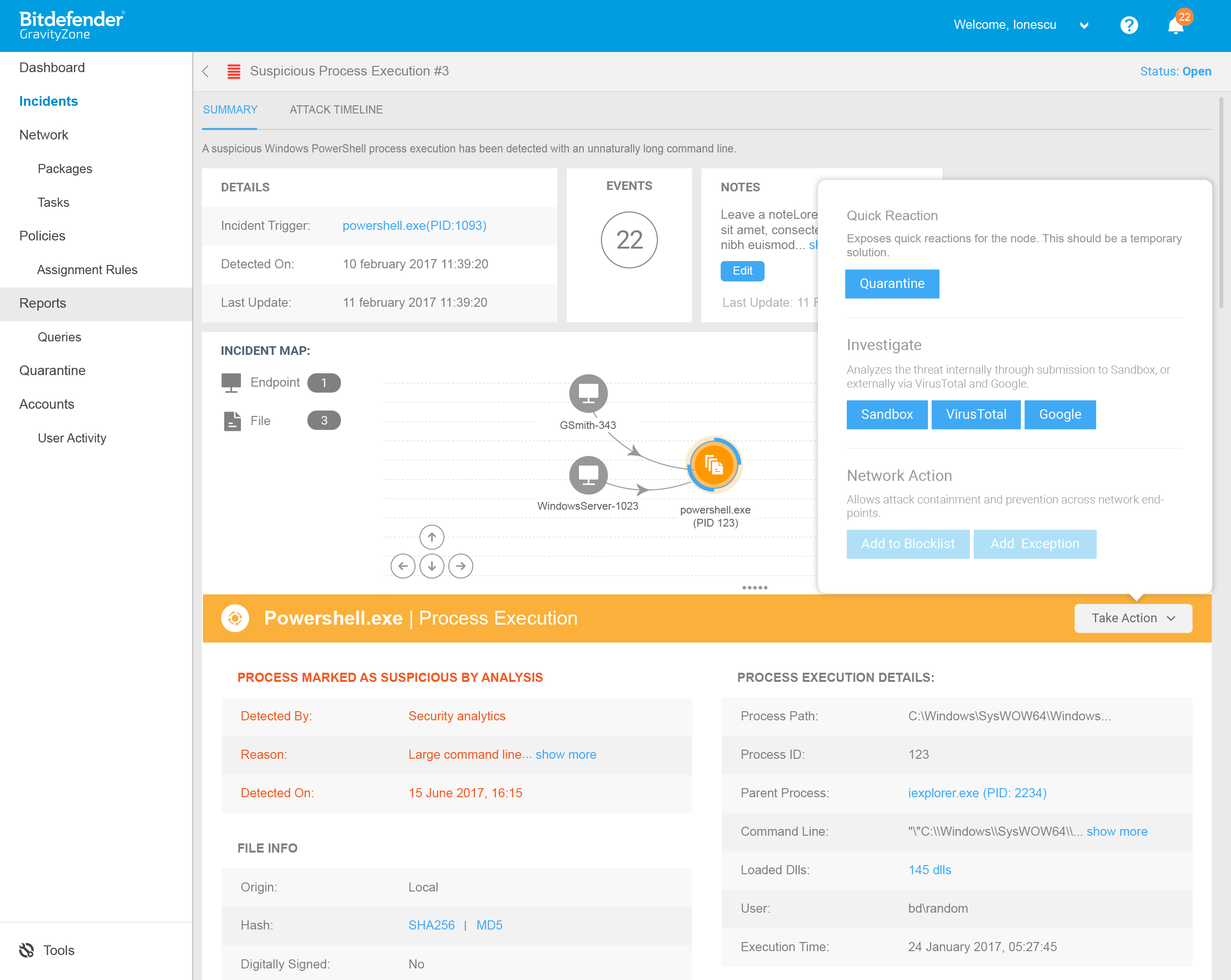
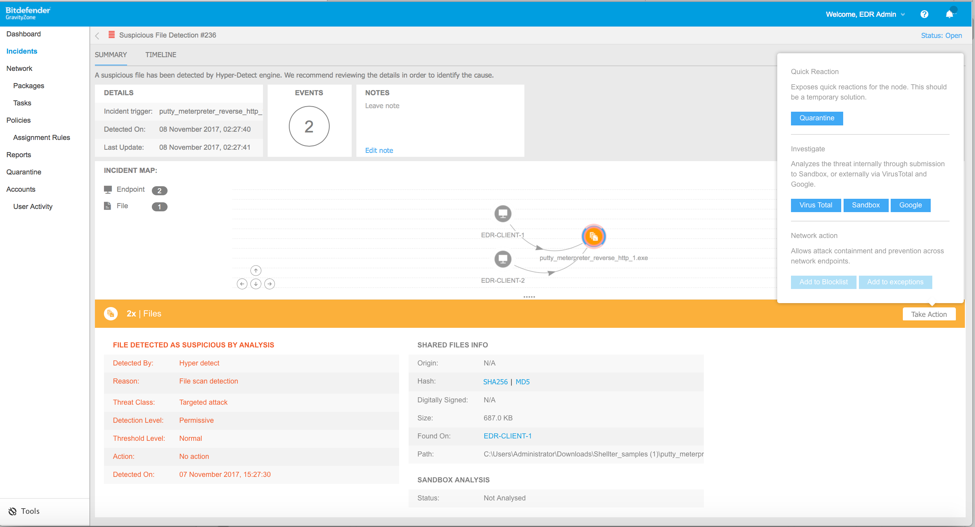
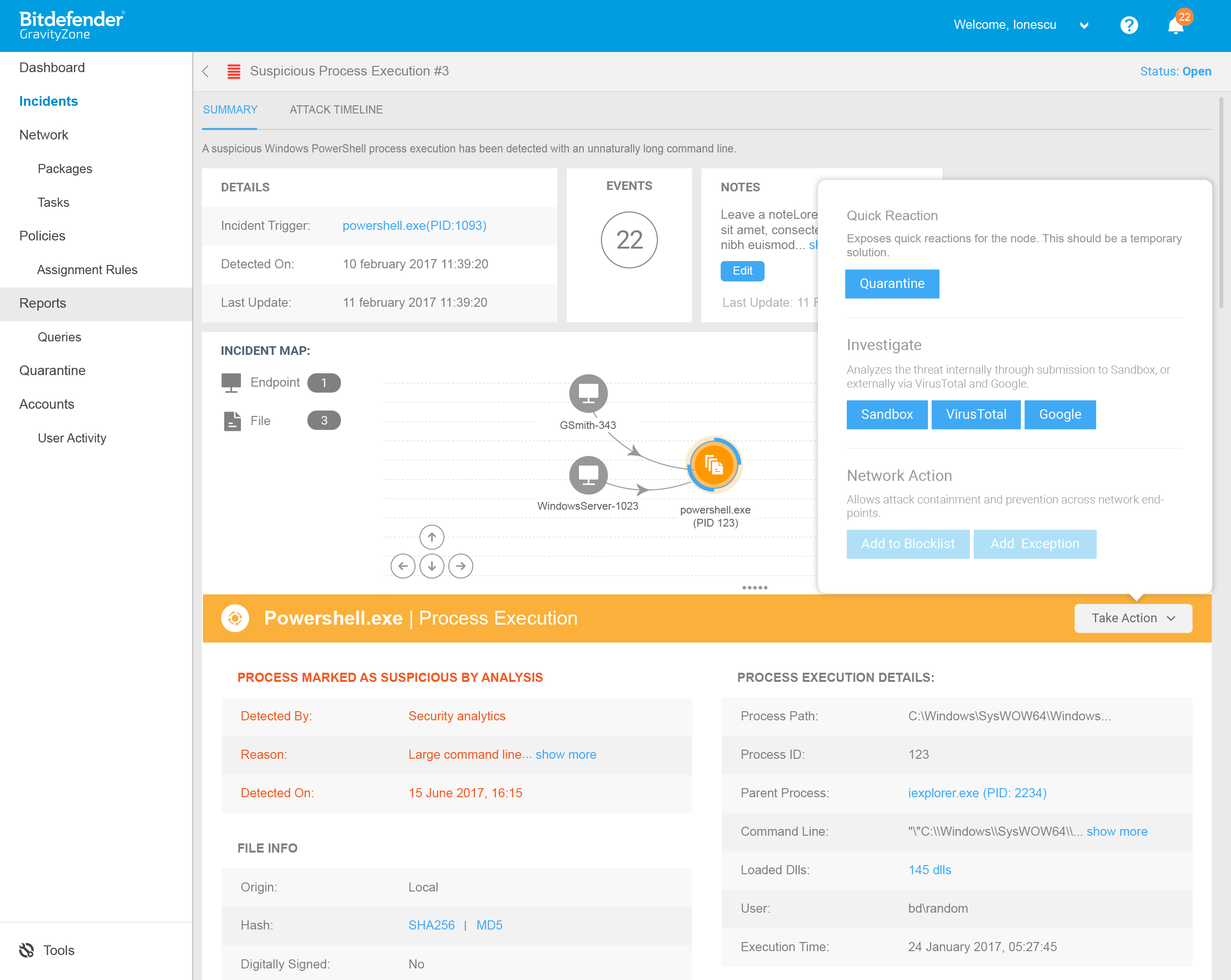
Investigate: aided by contextually relevant information on the class of threat that is detected (via the built-in intelligence), the reason of detection (via threat analytics), and ultimate verdict (via an integrated sandbox).
Respond: via a single pane of glass incident response interface that enables tactical remedial actions immediately and widely across the enterprise.
Evolve: enables the feedback loop from current detection to future prevention via in-place policy tuning and fortification.
GravityZone XDR, a single solution that also provides attack surface reduction (via firewall, application control, content control and patch management), data protection (via full disk encryption) and pre-execution detection and prevention of malware (via tunable machine learning, real-time process inspection and sandbox analysis), now adds automated detection, easy investigation and in-place remediation via the newly released endpoint data recorder and threat analytics components. The result: seamless threat prevention, accurate incident detection and smart response to minimize infection exposure and stop breaches.
Reach out to us if you want to see GravityZone XDR (via the GravityZone Ultra suite) in action in your organization.
tags
Author

Harish Agastya is VP of Enterprise Solutions at Bitdefender where he is responsible for the company’s enterprise business products and services portfolio. Agastya’s career spans over 25 years in high-tech B2B marketing, product management and R&D. Prior to joining Bitdefender, he held executive roles in marketing and products at other security companies. Agastya has an MBA from UC Berkeley and an MS in Computer Science from Penn State.
View all postsRight now Top posts
FOLLOW US ON SOCIAL MEDIA
SUBSCRIBE TO OUR NEWSLETTER
Don’t miss out on exclusive content and exciting announcements!
You might also like
Bookmarks