IoT botnets on the rise as the web now holds more bad bots than good

Hackers are moving away from cumbersome exploit kits and towards botnets after repeatedly leveraging new attack venues with a fair amount of success.
Gartner estimates there will be 20+ billion Internet of Things (IoT) products in the market by 2020, showing up in just about every aspect of life, from smart cities and buildings to smart home appliances and cars.
But while the concept of IoT promises improved productivity, longevity and enjoyment, it also opens a Pandora’s box of security issues, according to a new Radware report.
IoT – a threat landscape of unprecedented proportions
As connectivity and services move to the cloud, attackers are beginning to target IoT devices – and they have more than one reason for doing so. For one, embedded devices are easily exploitable, in the sense that many of them use default credentials or exposed services.
“IoT device manufacturers are focused on delivering solutions customers want at the lowest possible cost. Margins are the priority. There’s little regulatory control or oversight. Security features add development time and costs. Plus the ever-changing scope of attack types makes it impossible for manufacturers to address every possibility,” the report says.
Many off-the-shelf products also do not encrypt user passwords and fail to provide authentication for “remote configuration” services.
Second, always-on devices are available 24x7x365.
Third, malware leverages security controls (iptables, port filters) and kills service processes to prevent users from logging in or competing bots from taking control.
Fourth, IoT devices are rarely monitored and poorly maintained, which makes it easy for hackers to shut down or enlist large numbers of devices in a botnet for DDoS attacks.
“DDoS-for-hire services make it easy for anyone with malicious intent to launch an attack — whether they have technical savvy or not,” Radware researchers said.
For example, a group called Los Calvos de San Calvicie offers a DDoS attack of about 300 Gbps for only $20 per target.
Finally, the upcoming architecture of 5G networks is ideally suited for IoT devices that require low latency and fast data transmission, and its huge capacity is able to manage large numbers of concurrent device connections.
All these new devices create a threat landscape of unprecedented proportions, experts believe.
Forget exploit kits, bots are all the rage now
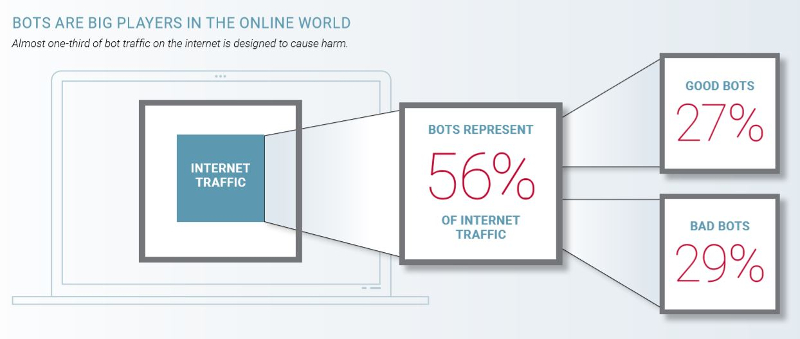
Exploit kits, a once popular attack avenue, are now barely used due to the popularity of other attack vectors. The same research uncovered that bots today are big players in the online world, making up a whopping 56% of all Internet traffic. Here’s where it gets interesting. Almost a third of bot traffic on the web is designed to cause harm, as the chart below shows.
Bad bots — including those that exploit internet of things (IoT) devices as weapons of attack — are one of the fastest-growing and changing threats in the security landscape. According to Daniel Smith writing on the company’s blog, cybercriminals are now following the money by taking the path of least resistance – botnets. This is because exploit kits are hard to maintain due to improved security practices and scarce exploits.
“Bad bot traffic is used for attacks on networks, servers, smartphones and connected devices to cause damage through DDoS, steal data, exploit intellectual property and purge inventory in online shops and ticketing systems,” researchers added.
Cybercriminals are also looking to maximize their infection rate by targeting insecure IoT devices with more than one payload, from crypto mining and ransomware to denial of service and fraud.
Finally, researchers also noticed an increasing number of botnets targeting enterprise devices, suggesting a growing interest in this sector on behalf of bad actors.
tags
Author
Filip has 15 years of experience in technology journalism. In recent years, he has turned his focus to cybersecurity in his role as Information Security Analyst at Bitdefender.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks








